Using SFTP with an SSH Agent
This guide is to help you when you want to setup an SFTP storage provider on bakup.io and use your servers SSH Agent to connect to another remote server, allowing you to keep your SSH keys on your server and let the SSH Agent handle authentication for you.
The SSH Agent is a Linux program which manages and holds your private keys that are used to connect to other networks and servers. Once you add an SSH key to the SSH Agent, when you connect to another server you won't have to tell it which key to use or even enter a password, the SSH Agent handles authentication for you. This is useful for non-interactive terminals and scripts that operate in the background, which is what the bakup agent does, it runs in the background and operates non-interactive terminals, so making use of the SSH Agent is great in this situation.
Starting your SSH Agent#
info
Because the bakup agent program creates its own service user called bakupagent and uses this user to operate in the background as a daemon, it executes jobs under the same service user. For the SSH Agent to work you will need to setup an SSH Agent for the bakupagent service user and not your own admin user etc.
To begin, you need to enable and start the SSH Agent program. To do this you can run the following commands:
Login as the bakup agent service user#
We will setup the SSH Agent for the service user because any jobs will run as this user.
Start the SSH Agent#
When you are logged in as the service user, launch the SSH Agent:
You can read more about ssh-agent and its options on the man page.
Once you have started the SSH Agent you will be given the PID of process, something like:
This means everything started successfully and you now have the SSH Agent running. You can configure the SSH Agent to run at login so that you don't have to manually start the process every time.
Configuring SSH Agent to Start at Login#
When you start the SSH Agent it will continue running in the background but if your server restarts or the agent process stops for some reason, it won't automatically start again, you would have to execute eval $(ssh-agent) to fix this.
It is possible to setup the SSH Agent to begin at login or during server boot, we recommend you find the best solution for your system but a few ways this can be done:
Inside of your
.bashrc,.profileor.bash_profileyou can setup scripts to launch the SSH Agent process if it is not running, but this method means you have to always login for the agent to be launched. Read more about this solution hereSetup a
systemdservice so that the SSH Agent can be started automatically during server boot. This method is more robust and can be setup to restart if the service fails. Read more about this solution here
Setting up the bakupagent home environment#
Following previous steps you should be logged in as the bakupagent service user, you should then create the bakupagent users home directory as its not created by default, you can do this by running:
Then you'll want to create the .ssh directory to store your private keys in:
Now you have a basic home directory setup, you should now transfer any private keys you wish to use with the SSH Agent inside of /home/bakupagent/.ssh. Make sure to also set the correct permissions for your key files.
Adding keys to the SSH Agent#
info
Remember that you will need to add private keys to the SSH Agent which is accessible to the bakup agent service user called bakupagent otherwise you will run into permission issues when jobs are executed.
Once you have the SSH Agent running you can start to add your private keys so that they can be used when connecting to another host.
For example to add a default key, you can run:
And to add a custom key to the agent:
Setting the SSH_AUTH_SOCK environment Variable#
When you have the SSH Agent started and keys added, you can check which Unix Socket the SSH Agent is using:
You'll need to take this filepath and save it inside of /home/bakupagent/.profile so that when the bakupagent user runs a job it knows where the SSH Agent is.
Inside of /home/bakupagent/.profile you should save it like so:
The .profile file is sourced whenever the bakup agent runs a job, it is set as a environmental variable, this is what allows the agent to know where the SSH Agent is.
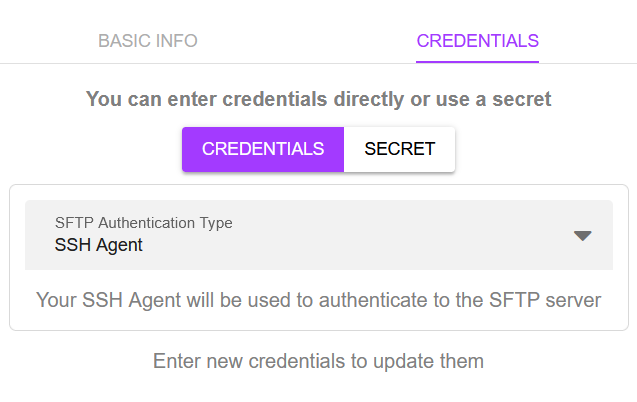
Using the SSH Agent Option on Bakup.io#
When you get to this stage and have set everything else up, you can select to use the SSH Agent as an authentication type for a SFTP storage provider:
Support#
Using the SSH Agent once setup is a great way to authenticate with different servers but can be a pain to setup, if you have followed the guide here and still have problems getting the SSH Agent method to work, get in touch and we can help: hello@bakup.io